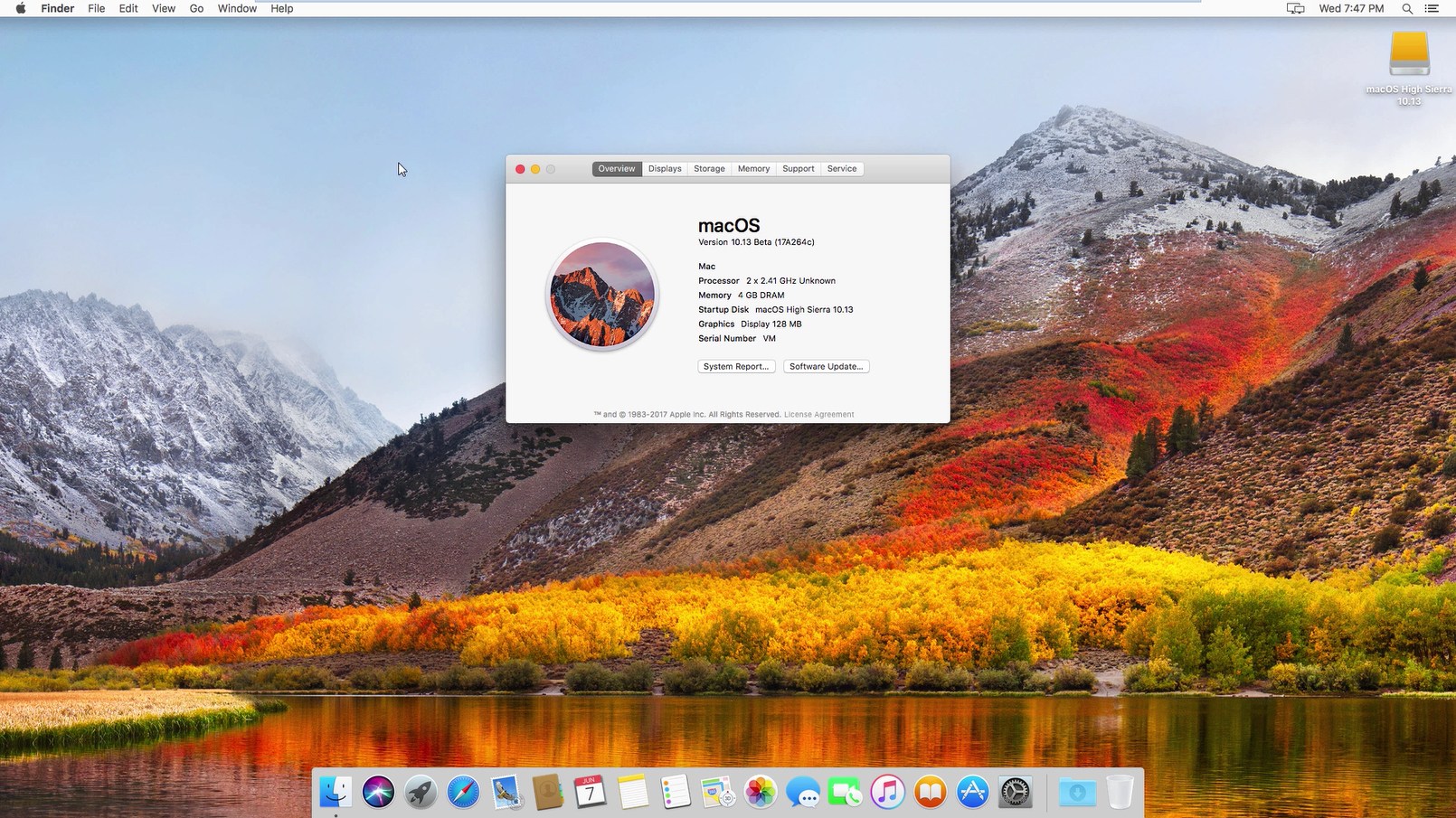
Apple starts rolling out latest updates for the entire suite of operating systems. After beta testing, the final versions including macOS High Sierra 10.13.3, iOS 11.2.5, and watchOS 4.2.2 are released officially. If you want to update multiple macOS systems, you can download macOS High Sierra 10.13.3 Offline Installer using direct download links. The latest build ships with version 17D47 or 17D2047 (depending on the machine).
The latest macOS High Sierra 10.13.3 addressed a problem in Messages where the conversation is listed out of order. Moreover, it also addressed an issue that could cause your Mac to stop responding when connected to an SMB server.
You can get macOS High Sierra 10.13.3 either through Mac App Store or download macOS High Sierra 10.13.3 DMG file using official links provided in this post.
“The macOS High Sierra 10.13.3 Update improves the stability and security of your Mac and is recommended for all users”, Apple says.
Changelog of macOS High Sierra 10.13.3 Update
- Addresses an issue that could cause Messages conversations to temporarily be listed out of order
- Resolves an issue that could cause your Mac to stop responding when connected to an SMB server
macOS High Sierra 10.13.3, Security Update 2018-001 Sierra, and Security Update 2018-001 El Capitan
Audio
Download Macos High Sierra 10.13.6
Download macOS High Sierra 10.13.2 Supplemental. The macOS High Sierra 10.13.2 Supplemental Update provides a security update and is recommended for all users.
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6
- MacOS High Sierra 10.13.2 improves certain features of Apple’s operating system for laptops and computers, so users are advised to download and install the software update as soon as it becomes.
- 3 – unizp macOS.High.Sierra.10.13.6.part1.rar with winzip but it doesn’t work, it doesn’t ask me the password but instead it creates another macOS.High.Sierra.10.13.6.part1.rar file second attempt. 1 – downloaded 5 macOSHighSierra.rar file on a windows pc into the same folder 2 – downloaded winzip tool on windows pc.
Impact: Processing a maliciously crafted audio file may lead to arbitrary code execution
Description: A memory corruption issue was addressed through improved input validation.
CVE-2018-4094: Mingi Cho, MinSik Shin, Seoyoung Kim, Yeongho Lee and Taekyoung Kwon of the Information Security Lab, Yonsei University
curl
Available for: macOS High Sierra 10.13.2
Impact: Multiple issues in curl
Description: An out-of-bounds read issue existed in the curl. This issue was addressed through improved bounds checking.
CVE-2017-8817: found by OSS-Fuzz
IOHIDFamily
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2018-4098: Siguza
Kernel
Available for: macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to read kernel memory (Meltdown)
Description: Systems with microprocessors utilizing speculative execution and indirect branch prediction may allow unauthorized disclosure of information to an attacker with local user access via a side-channel analysis of the data cache.
CVE-2017-5754: Jann Horn of Google Project Zero; Moritz Lipp of Graz University of Technology; Michael Schwarz of Graz University of Technology; Daniel Gruss of Graz University of Technology; Thomas Prescher of Cyberus Technology GmbH; Werner Haas of Cyberus Technology GmbH; Stefan Mangard of Graz University of Technology; Paul Kocher; Daniel Genkin of University of Pennsylvania and University of Maryland; Yuval Yarom of University of Adelaide and Data61; and Mike Hamburg of Rambus (Cryptography Research Division)
Kernel
Available for: macOS High Sierra 10.13.2
Impact: An application may be able to read restricted memory
Description: A memory initialization issue was addressed through improved memory handling.
CVE-2018-4090: Jann Horn of Google Project Zero
Kernel
Available for: macOS High Sierra 10.13.2
Impact: An application may be able to read restricted memory
Description: A race condition was addressed through improved locking.
CVE-2018-4092: an anonymous researcher
Kernel
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: A malicious application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed through improved input validation.
CVE-2018-4082: Russ Cox of Google
Kernel
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A logic issue was addressed with improved validation.
CVE-2018-4097: Resecurity, Inc.
Kernel
Available for: macOS High Sierra 10.13.2
Impact: An application may be able to read restricted memory
Download Macos 10.13.6
Description: A validation issue was addressed with improved input sanitization.
CVE-2018-4093: Jann Horn of Google Project Zero
LinkPresentation
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6.2
Impact: Processing a maliciously crafted text message may lead to application denial of service
Description: A resource exhaustion issue was addressed through improved input validation.
CVE-2018-4100: Abraham Masri (@cheesecakeufo)
QuartzCore
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: A memory corruption issue existed in the processing of web content. This issue was addressed through improved input validation.
CVE-2018-4085: Ret2 Systems Inc. working with Trend Micro’s Zero Day Initiative
Sandbox
Available for: macOS High Sierra 10.13.2
Impact: A sandboxed process may be able to circumvent sandbox restrictions
Description: An access issue was addressed through additional sandbox restrictions.
CVE-2018-4091: Alex Gaynor of Mozilla
Security
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6
Impact: A certificate may have name constraints applied incorrectly
Description: A certificate evaluation issue existed in the handling of name constraints. This issue was addressed through improved trust evaluation of certificates.
Download Macos 10.13 Installer
CVE-2018-4086: Ian Haken of Netflix
WebKit
Available for: macOS High Sierra 10.13.2
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2018-4088: Jeonghoon Shin of Theori
CVE-2018-4089: Ivan Fratric of Google Project Zero
CVE-2018-4096: found by OSS-Fuzz
Wi-Fi
Available for: macOS High Sierra 10.13.2, macOS Sierra 10.12.6, OS X El Capitan 10.11.6
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2018-4084: Hyung Sup Lee of Minionz, You Chan Lee of Hanyang University
Download macOS High Sierra 10.13.3 Offline Installer
macOS High Sierra 10.13.3 DMG – Download (Size: 1.9 GB)
Download Security Update 2018-001 macOS Sierra Offline Installer
Security Update 2018-001 macOS Sierra DMG – Download (Size: 731 MB)
Download Security Update 2018-001 (El Capitan) Offline Installer
Security Update 2018-001 (El Capitan) OS X – Download (Size: 823 MB)
